Filters
AI Models
Assistants APICustom GPTsOpenGPTsGemini AIPineconeTogether AIUnstructured IOSDXL TurboAI/ML APIwatsonx.aiTinyLlamaGemma 2AutoGenBabyAGIOpenAIGPT-3.5LTM-2-miniRestackSambaNovaGroqCohere RerankGPT-4 VisionDALL·E Image Generation APIStableCodeStable DiffusionPortkeyTonic.aiLlama 3IBM GraniteUpstageSuperAGILlama 3.1o1ClarifaiCodiumopen-interpreterGrounded-Segment-AnythingprivateGPTGorillaGenerative AgentsMistral AIFuyu-8BYi-LLMSChatGPTArizeGET3DOpenELMFalcon 2 11BAgentOpsWeaviateGenerative AI StudioOpenAI gymImagenAudioCraftLlama 3.2LlamaIndexGodmode AIIBM watsonx AssistantPaLMDall-e MiniGPT-3CodexYOLOv7BERTYOLOv5GANReinforcement LearningYOLOv6AWS SageMakerEasyOCRCAMELText Generation Web UIShap-EDALL-E-2AI21 LabsCohere EmbedChirpWhisperWebGPUMonday AI AssistantMonday.comVectorboard 💛ChromaCohere GenerateCohere ClassifyGPT-4AlpacaCohere Neural SearchLLaMAAuto-GPTAnthropic ClaudeYOLOv8gpt4allFalconCodeyModel GardenElevenLabsLlama 2Point-EStable DreamfusionZillizSeamlessM4TMetaGPTStable LMTwelve LabsFalcon 2 11B VLMComposioPhi-3GemmaGPT 4oGrokToolhouseCAMEL-AIDeepSeek R1DeepSeek V3Trae IDELlama 4GPT-5Cohere Coral
Data
Platforms
AI Models
Assistants APICustom GPTsOpenGPTsGemini AIPineconeTogether AIUnstructured IOSDXL TurboAI/ML APIwatsonx.aiTinyLlamaGemma 2AutoGenBabyAGIOpenAIGPT-3.5LTM-2-miniRestackSambaNovaGroqCohere RerankGPT-4 VisionDALL·E Image Generation APIStableCodeStable DiffusionPortkeyTonic.aiLlama 3IBM GraniteUpstageSuperAGILlama 3.1o1ClarifaiCodiumopen-interpreterGrounded-Segment-AnythingprivateGPTGorillaGenerative AgentsMistral AIFuyu-8BYi-LLMSChatGPTArizeGET3DOpenELMFalcon 2 11BAgentOpsWeaviateGenerative AI StudioOpenAI gymImagenAudioCraftLlama 3.2LlamaIndexGodmode AIIBM watsonx AssistantPaLMDall-e MiniGPT-3CodexYOLOv7BERTYOLOv5GANReinforcement LearningYOLOv6AWS SageMakerEasyOCRCAMELText Generation Web UIShap-EDALL-E-2AI21 LabsCohere EmbedChirpWhisperWebGPUMonday AI AssistantMonday.comVectorboard 💛ChromaCohere GenerateCohere ClassifyGPT-4AlpacaCohere Neural SearchLLaMAAuto-GPTAnthropic ClaudeYOLOv8gpt4allFalconCodeyModel GardenElevenLabsLlama 2Point-EStable DreamfusionZillizSeamlessM4TMetaGPTStable LMTwelve LabsFalcon 2 11B VLMComposioPhi-3GemmaGPT 4oGrokToolhouseCAMEL-AIDeepSeek R1DeepSeek V3Trae IDELlama 4GPT-5Cohere Coral
Data
Platforms
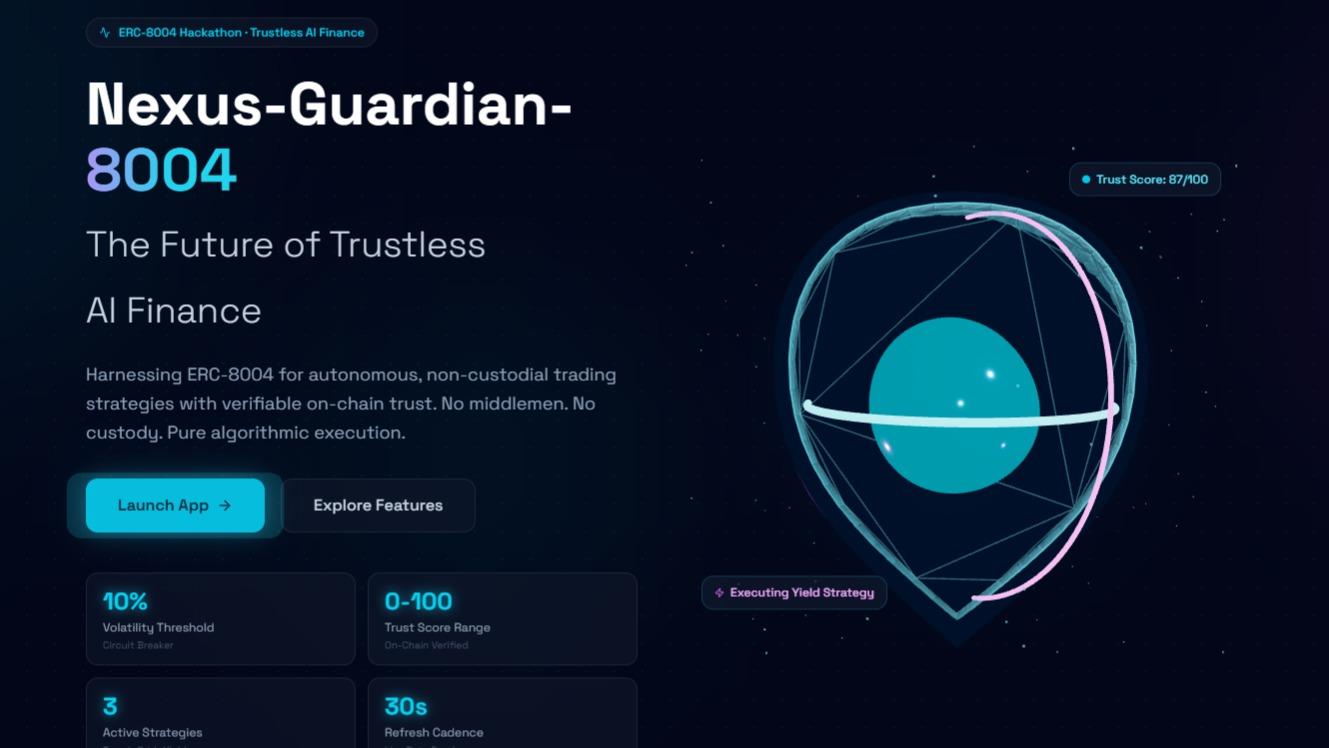
Upcoming AI Hackathons
For Innovators & Creators
For Innovators & Creators
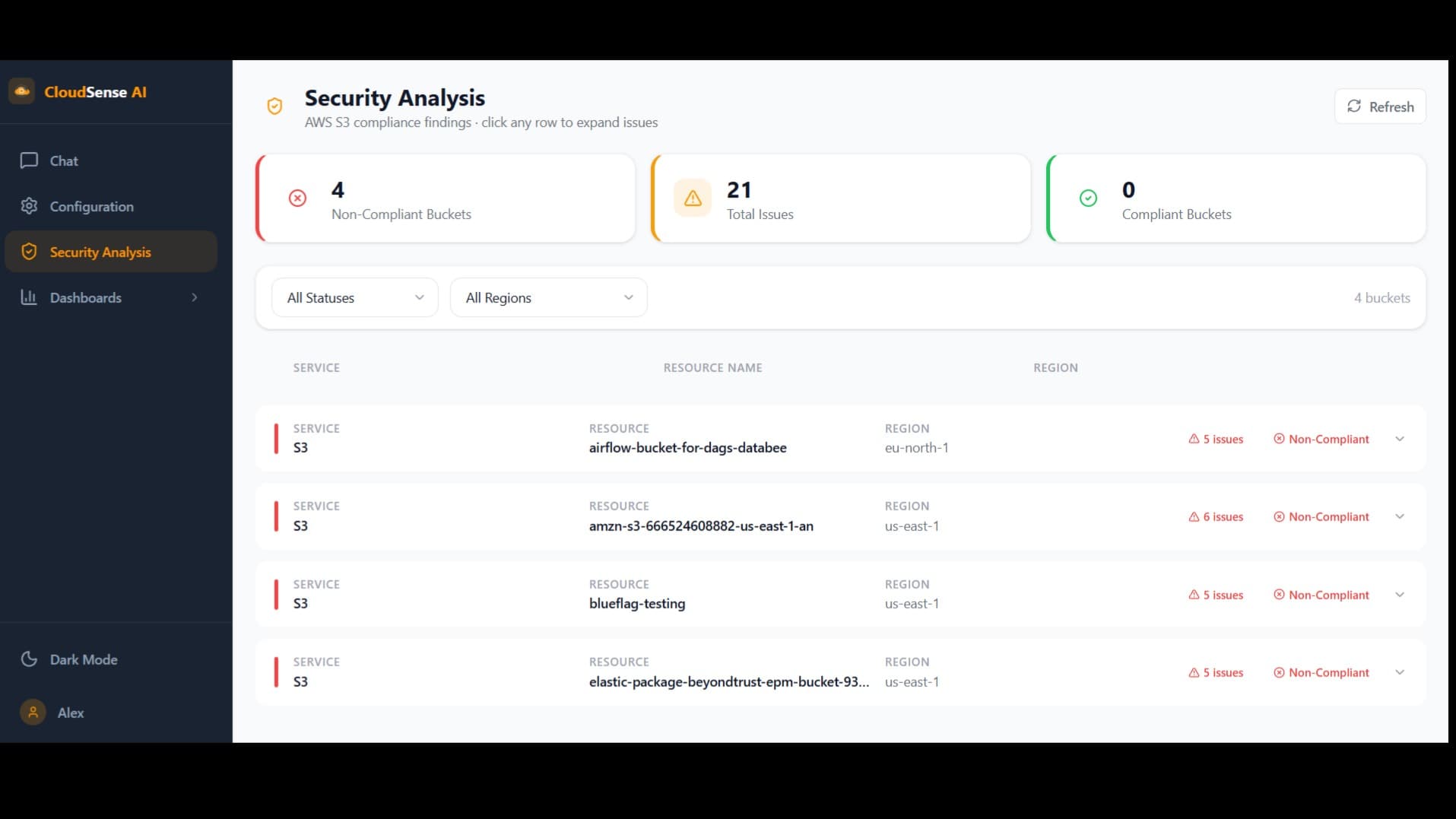
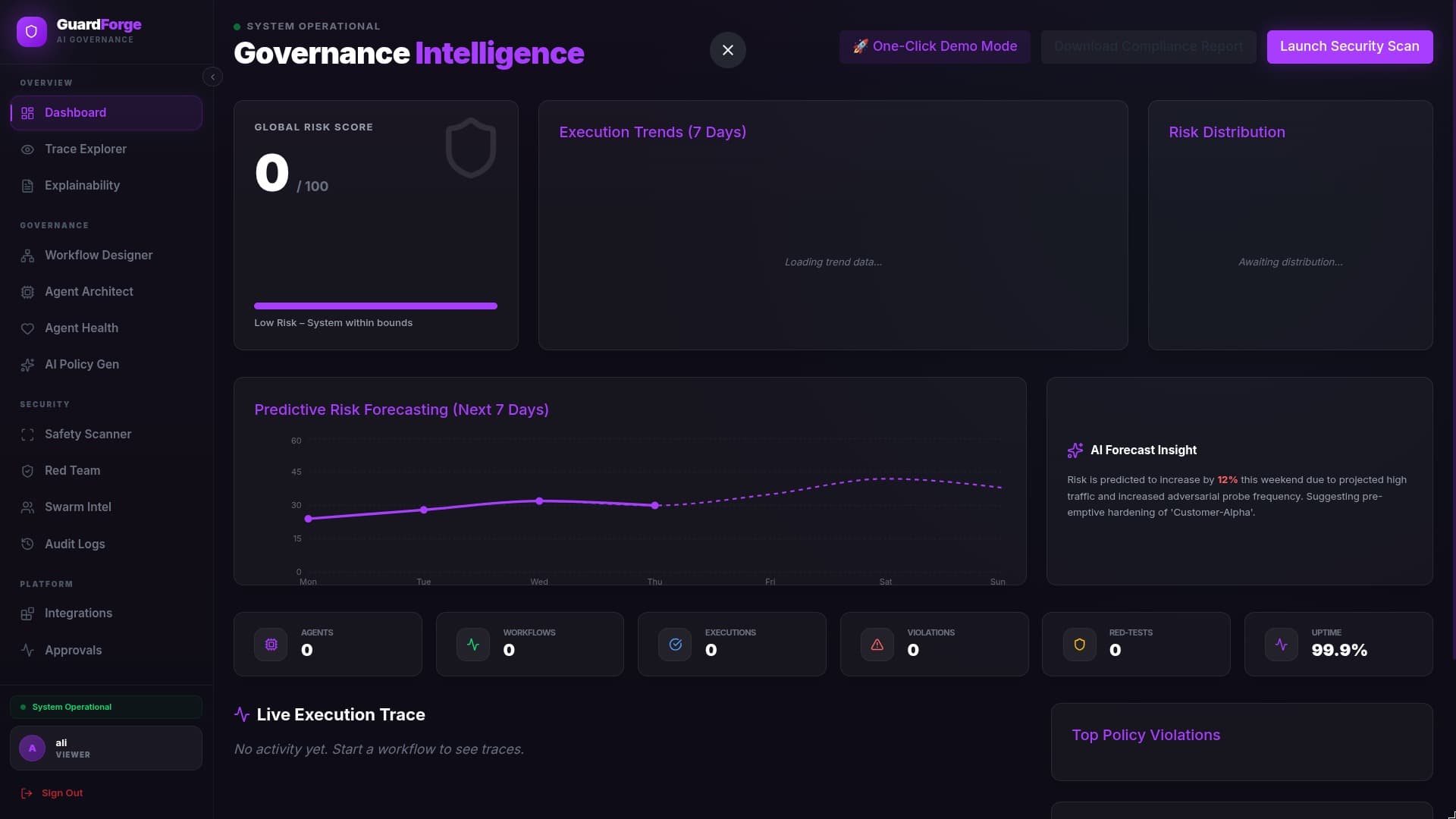
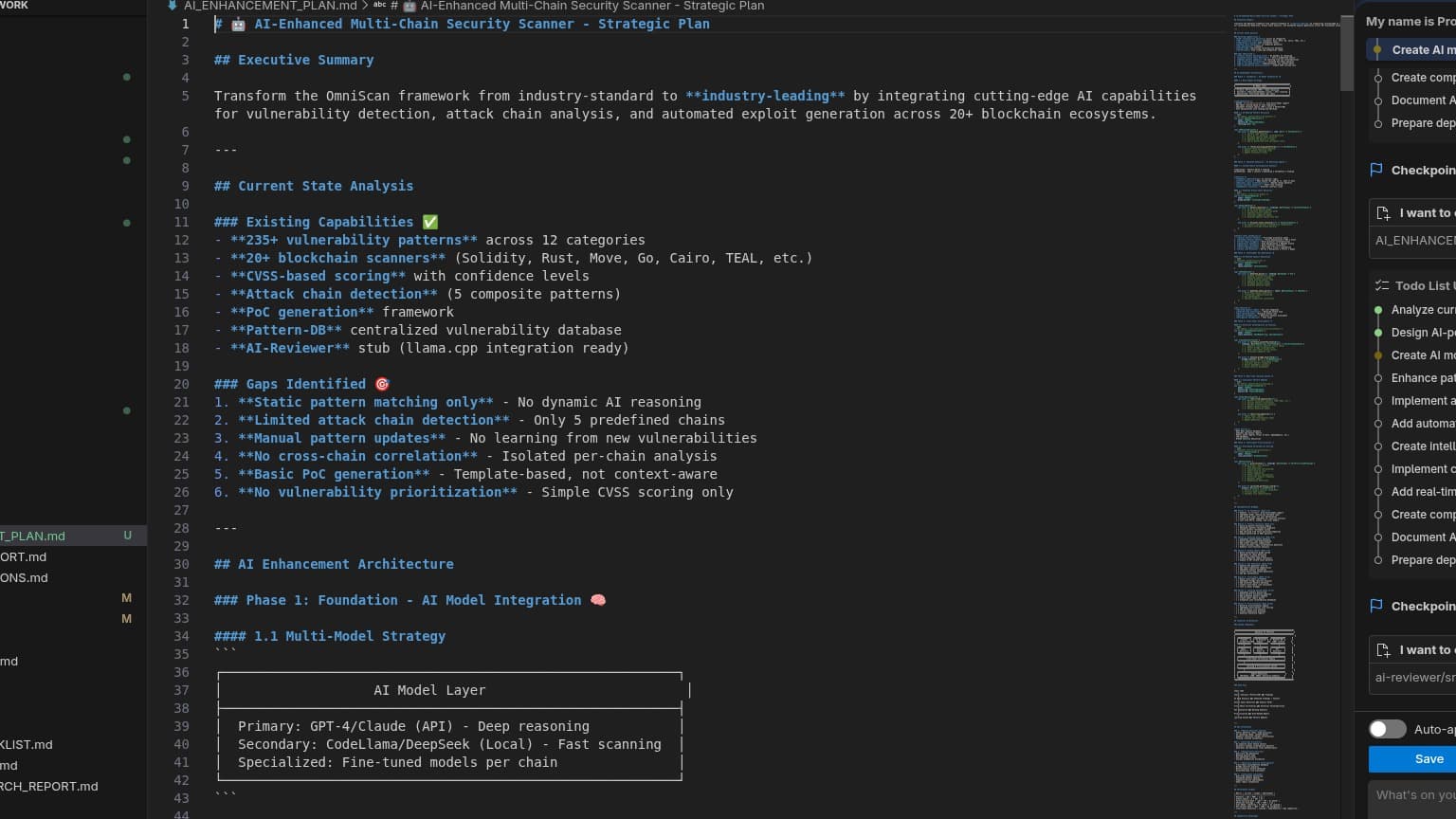
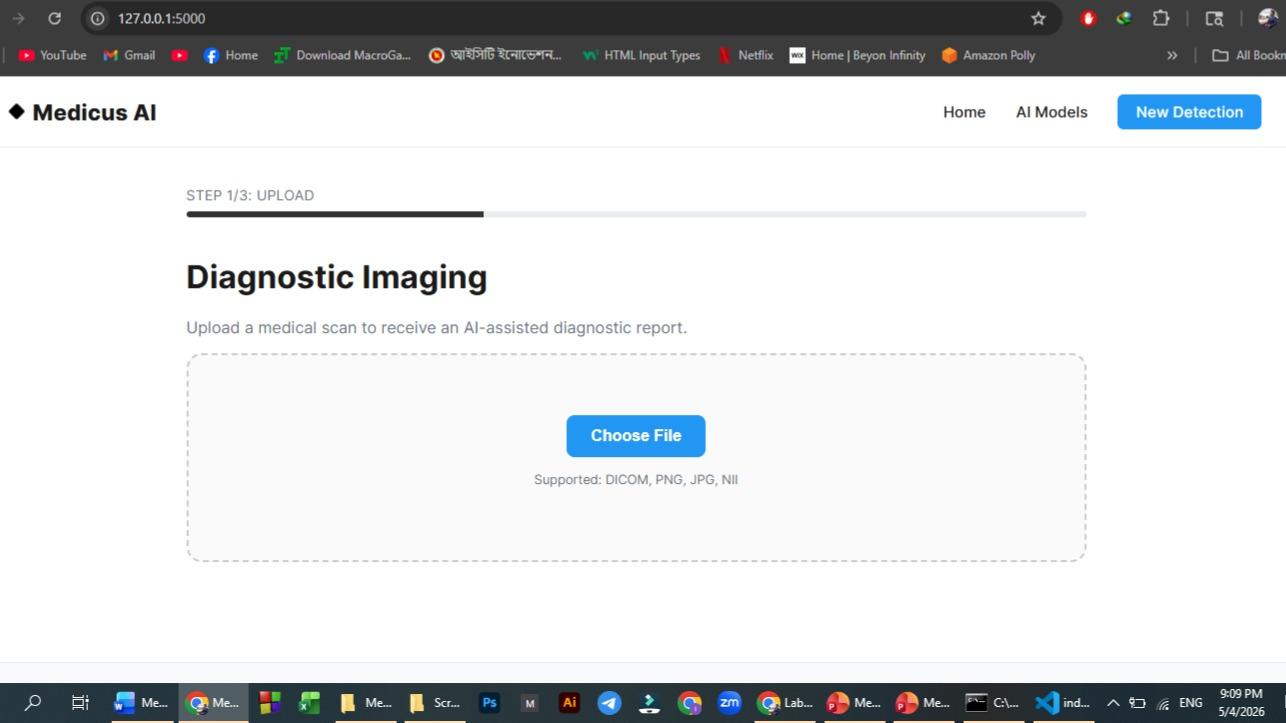
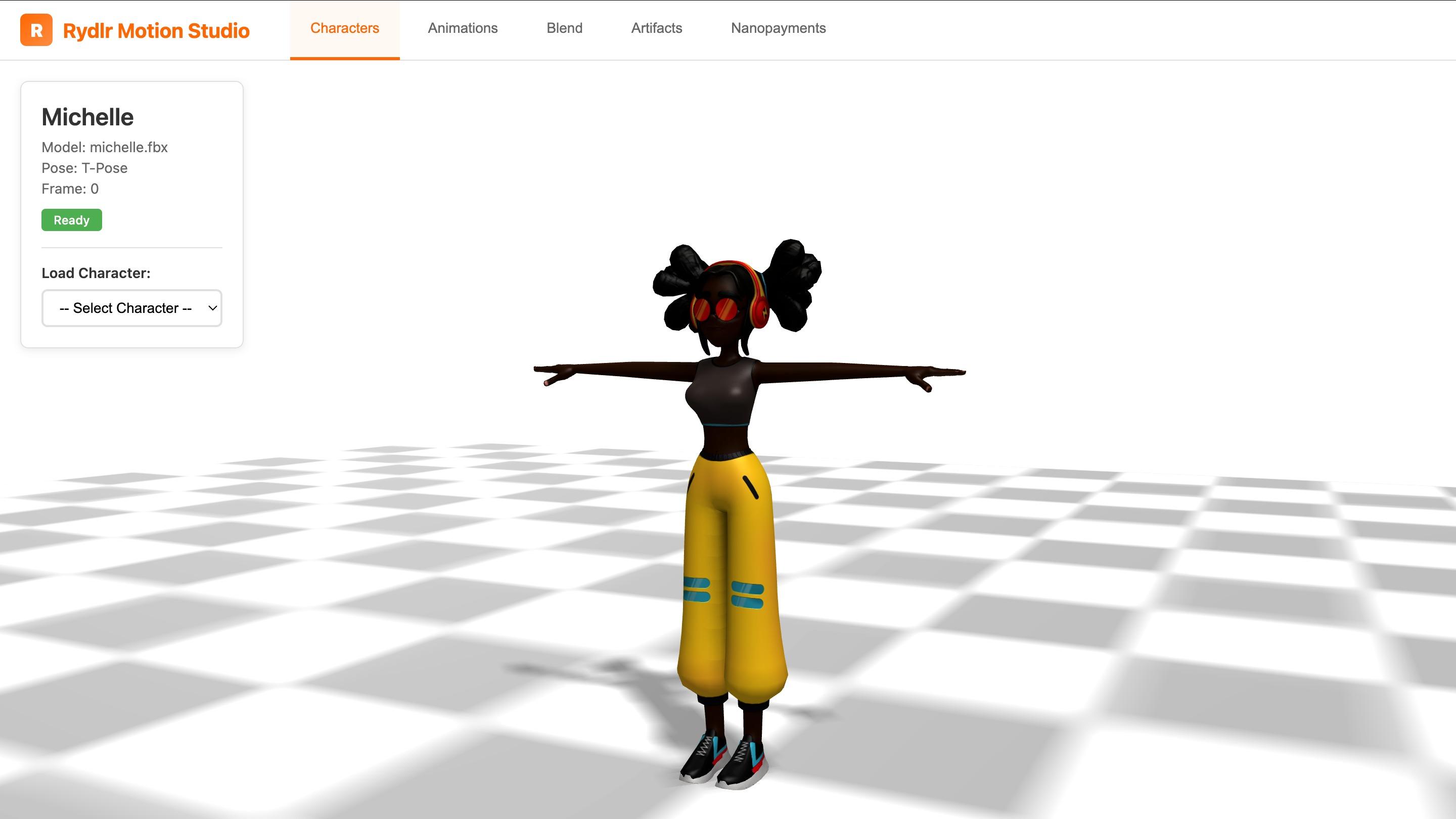
Discover AI Applications
Browse applications built on modern technologies. Explore PoC and MVP applications created by our community and discover innovative use cases for modern technologies.
All apps loaded
494apps · all done






























.png&w=3840&q=75)








.png&w=3840&q=75)



















.png&w=3840&q=75)

.png&w=3840&q=75)






















.png&w=3840&q=75)











































.png&w=3840&q=75)




















.png&w=3840&q=75)









.png&w=3840&q=75)









.png&w=3840&q=75)










































.png&w=3840&q=75)




































































.png&w=3840&q=75)



.png&w=3840&q=75)
.png&w=3840&q=75)






























.png&w=3840&q=75)




.png&w=3840&q=75)

























.png&w=3840&q=75)