Duc Nguyen@vanduc2514
2
Events attended
2
Submissions made
Viet Nam
6+ years of experience
About me
Software engineer passionate about developer tools, backend systems, and AI-assisted workflows. Interested in building practical AI experiences that help developers automate repetitive tasks, better understand complex codebases, and ship software more effectively. Currently exploring AI agents, workflow automation, and developer-focused tooling that makes AI a more reliable engineering partner in real-world software development.
🤝 Top Collaborators
🤓 Latest Submissions
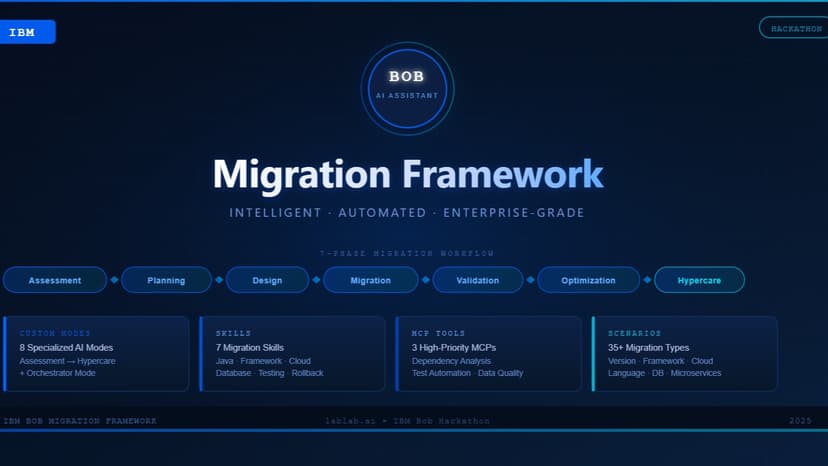
Assisted Migration Framework with IBM Bob
This project enhances IBM Bob with specialized skills and custom operating modes that enable it to orchestrate and execute complex technical migrations with precision, automation, and intelligence. Leveraging the 7Rs Migration Framework, Bob analyzes an organization’s current systems, architecture, dependencies, and business requirements to recommend the most suitable migration strategy, including rehost, replatform, repurchase, refactor/re-architect, retire, retain, or relocate. Beyond strategy selection, Bob supports the entire migration lifecycle by producing detailed migration designs and implementation plans, performing dependency mapping, impact and risk analysis, resource and timeline estimation, rollback preparation, and technical documentation generation. During execution, Bob automates migration activities such as code transformation and refactoring, configuration and environment updates, dependency upgrades, infrastructure provisioning through Infrastructure as Code, and deployment automation integrated with CI/CD pipelines. To ensure migration quality and reliability, Bob also handles validation through automated testing, security and code quality analysis, performance benchmarking, data integrity verification, and functional and integration testing. After deployment, Bob continues to provide hypercare support with real-time monitoring, alerting, performance optimization recommendations, issue detection and resolution guidance, knowledge transfer, documentation maintenance, and continuous improvement insights to help teams stabilize and optimize their modernized platforms.
17 May 2026

ATOMiK Constitution Review
ATOMiK is a constitutional control plane for coding agents: it does not just show agents doing work; it shows them being constrained. The demo seeds a subtle bad PR that bypasses a protected-ref policy. A baseline reviewer approves it. ATOMiK then runs three legislative-branch agents, commits structured proposal artifacts on real Git worktrees, uses git merge-tree --write-tree to produce executive candidate state, scores the delta through an ATOMiK C ABI stub, and sends governance metadata to a Lean-backed judiciary. The judiciary vetoes unsafe dispatch, preserves the protected ref, and records the audit trail in JSONL, Git metadata, signed/simulated constitutional epoch tags, and a live dashboard. The model layer targets AMD MI300X-hosted coding-agent inference via ROCm and an OpenAI-compatible vLLM endpoint, with deterministic fallback to keep the governance proof reliable during judging. Business buyers are platform engineering, AppSec, and DevSecOps teams adopting coding agents in repositories where protected branches, audit evidence, and rollback matter. The first product is a GitHub/GitLab app that blocks agent-authored protected-ref or policy-sensitive changes unless they include a signed judiciary ruling artifact. Orchestrators route tasks, AgentOps tools observe traces, and guardrails flag risky text. ATOMiK decides whether an agent-authored repository state transition may advance protected authority. The model can change; the constitution still wins.
10 May 2026
.png&w=640&q=75)
.png&w=640&q=75)


