🤝 Top Collaborators
🤓 Latest Submissions
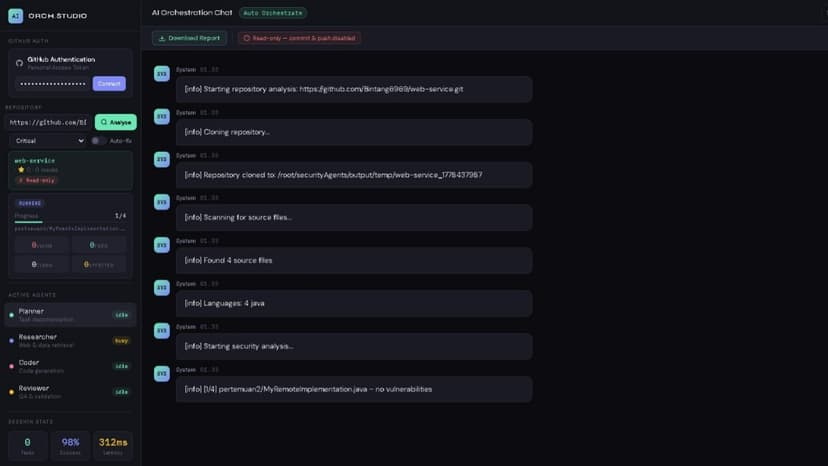
Security Council AI Agents and Fine-Tuned Models
Security Council AI is a dual-track system combining AI Agent orchestration with specialized fine-tuned models for end-to-end code security automation. Built natively for AMD ROCm 7.0 hardware, it completely eliminates CUDA translation overhead. Track 1: AI Agents Architecture We implemented a multi-agent workflow in lightweight Python. A Router Agent classifies incoming requests. An Auditor Agent detects vulnerabilities and provides mitigation strategies in structured JSON. A Builder Agent generates secure code patches. Finally, an Orchestrator Agent merges outputs and handles fallbacks. This setup enables autonomous task routing, multi-step reasoning, and tool calling without heavy external framework dependencies. Track 2: Fine-Tuning Methodology Using Qwen2.5-Coder-14B-Instruct as our base model, we fine-tuned two specific models using LoRA (r=64, alpha=128) in float16 precision for ROCm kernel stability. We curated two datasets of 4,622 examples each: one for CVE/CWE detection and another for secure patch generation. Critical ROCm 7.0 optimizations were applied, such as HSA_OVERRIDE_GFX_VERSION=11.0.0 and specific PyTorch memory allocation flags (expandable_segments:False) to prevent allocator deadlocks on MI300X GPUs. Integration and Impact By splitting tasks across specialized models coordinated by an agent layer, we achieve superior accuracy over generalist models. The system works seamlessly: the Auditor identifies the CWE, and the Builder uses that context to generate a precise patch. The system exposes OpenAI-compatible APIs and offers a one-click Docker deployment. Released under the Apache 2.0 license, Security Council AI reduces vulnerability-to-fix time from days to seconds, enables security-as-code in CI/CD pipelines, and provides a practical blueprint for deploying large models on the AMD hardware ecosystem.
10 May 2026
.png&w=256&q=75)


.png&w=640&q=75)
